In a centralized system, all computers connected to a server refer to the information present on the central server, and whoever controls the server controls the state of the system. Changing this paradigm is incredibly difficult. It’s not just about implementing a new type of encrypted information on private computers; it’s about creating a new system for managing decisions among peer computers. While developing this system, one must consider the possibility of individuals with malicious intent, tampered or malfunctioning computers – in short, it’s a truly complex challenge.
In a decentralized system, the concept of consensus is fundamental. That is, how do computers agree to decide the state of the system? We have seen how consensus is managed in a centralized system: simply, the state of the system is decided by the central server, which everyone must trust. The information is saved, modified, and read by a single computer, the server.
The first form of consensus in a decentralized system was Proof of Work, published in 2008 in the article that first introduced Bitcoin. Proof of Work is based on a very simple postulate: the most powerful computer in a decentralized system is much less powerful than the sum of all other computers in the network. The network implementing Proof of Work works in shifts. Whenever a decision needs to be made, all computers generate the same mathematical challenge. The first to solve the challenge acts as the central server for that turn, and then the next turn and decision follow. If there are 100 computers in the network, and all computers have roughly the same computing power, a different computer will win each turn. A computer that wants to win every challenge would have to be more powerful than all the others combined, making the endeavor virtually impossible. Proof of Work brings another important benefit to the decentralized network: making a decision requires effort. The malevolent individual who wants to insert a corrupt state into the system must invest a lot of resources to succeed.
Some will have surely noticed a problem: what happens if a malicious computer wins a turn? The system’s state would be corrupted in that turn. Bitcoin solves this flaw by allowing the winner of the subsequent challenge to create a parallel state. In this case, the system will end up with two states. How to manage this situation? Simply, the next winner can decide on which of the two states to make the modification. The state with more modifications will be the one in which the majority of computers have decided to invest resources and therefore considered the “official” one.
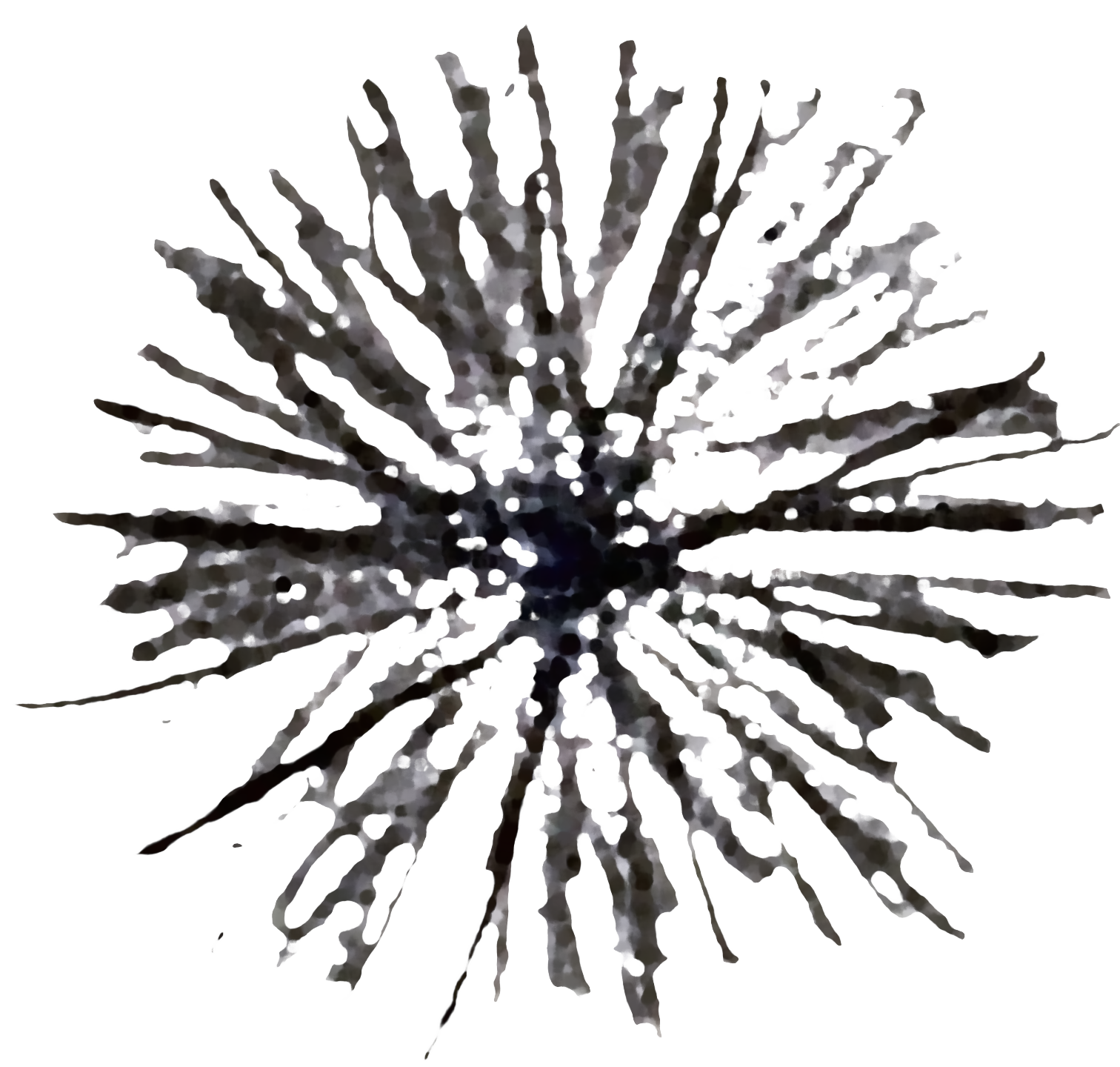
In the previous figure, the red circle represents the state created by the malicious computer, while the circle on the far right represents the system’s “official” state. Each line is a modification that connects the previous state to the next. The reader can now imagine the reason behind the name blockchain, i.e., a chain of blocks. Each state, or block, is connected to the previous one. The chain can fork in the case where a malicious computer creates a state to which no other computer wants to attach a subsequent state.
All that remains is to understand the role of cryptography in the blockchain to have a fairly complete idea of Bitcoin’s functioning. To do this, we must create a new type of safe in which there is not only one key but two opposite ones: the usual secret key and a new public key available to everyone. When the safe is closed with one of the two keys, it can then only be opened with the opposite. This allows new use cases for our digital safes. For example, Marco closes a message in Matteo’s safe using Matteo’s public key. This message can only be read by Matteo, who will use his secret key to open the safe. Conversely, Matteo closes his safe with his private key. Everyone can open his safe (because Matteo’s public key is public), but they will have a guarantee: the safe was definitely closed by Matteo. And this is the missing piece to complete the puzzle: the digital signature. With this new type of safes, which we will call asymmetric cryptography, it is possible to sign a message using one’s private key because that message can only be read using the public key opposite the private key used.
At this point, the reader will be tired; the manual has been pedantic in describing the fundamental properties of Bitcoin. Unfortunately, without this information, it is impossible for the primitive to evolve to better survive within the digital world. However, one can finally understand the true revolution of the blockchain: a central server is no longer necessary to program information.
The implications are immense. If in the centralized system the bank acted as the guarantor of human financial information, in the decentralized system there is no longer a single guarantor, and the integrity of the information is guaranteed by the method of consensus and cryptography. Homo sapiens can finally start thinking about moving the information of their cave’s ownership to a safer place, a place from which no centralized entity can alter their personal data. Unfortunately, Bitcoin is a system specifically designed for currency management and does not support generic programming or all types of information. Therefore, humans will have to wait a little longer before securing their caves. In the meantime, however, they can abandon their bank and move their funds to the blockchain.